Wir helfen Software zu entwickeln

Product Owner für interne IT-Security Systeme
Als Product Owner technisch anspruchsvolle IT-Security Produkte entwickeln.
Produktentwicklung
Softwareentwicklung
Digitalisierung
Product Owner
Mehr erfahren

Product Owner für eine integrierte E-Commerce Systemlandschaft
Als Product Owner nachhaltige Softwareentwicklung und Betrieb sicherstellen.
Digitalisierung Geschäftsprozesse
Product Owner
Mehr erfahren

Interim Product Owner für eine Lernplattform
Interim Product Owner und Agile Coach für die Entwicklung einer inaktiven Lernplattform für Samsung.
Digitalisierung
Softwareentwicklung
Produktentwicklung
Scrum Master
Product Owner
Mehr erfahren

Beratung, Architektur und Migration von zentraler Software-Komponente
Mit nachhaltiger Beratung und technischer Expertise zentrale Software-Komponente erfolgreich abgelöst.
Mittelstand
Projektorganisation
Prozessoptimierung
Mehr erfahren
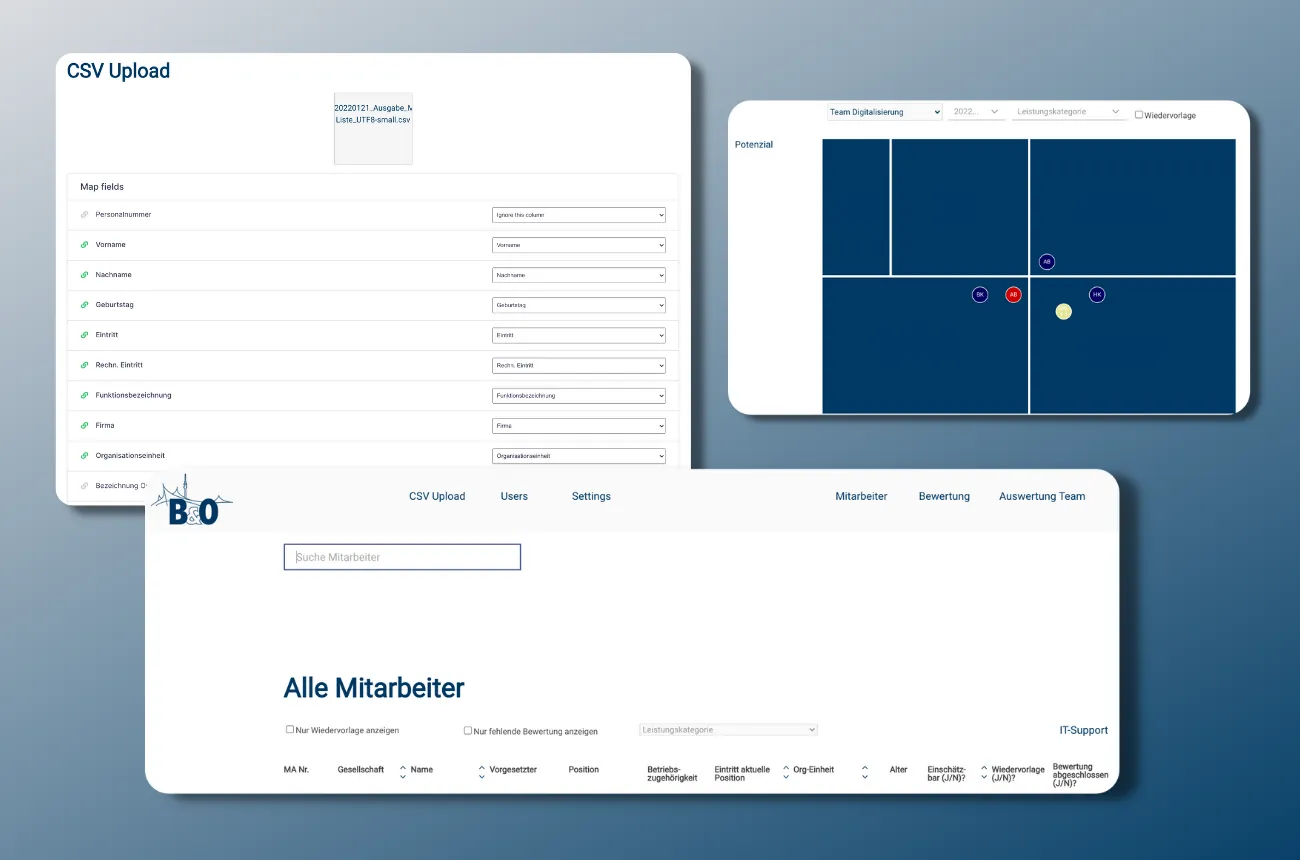
HR-Applikation für Mitarbeiterbewertung
Excelformulare für die Mitarbeiterbewertung? Mit optimierten und digitalisierten Prozesse Zeit gespart.
Prozessoptimierung
Mittelstand
Mehr erfahren